SOAP (Simple Object Access Protocol)
What is SOAP (Simple Object Access Protocol)?
SOAP (Simple Object Access Protocol) is a message protocol that enables the distributed elements of an application to communicate. SOAP can be carried over a variety of standard protocols, including the web-related Hypertext Transfer Protocol (HTTP).
SOAP was developed as an intermediate language for applications that have different programming languages, enabling these applications to communicate with each other over the internet. SOAP is flexible and independent, which enables developers to write SOAP application programming interfaces (APIs) in different languages while also adding features and functionality.
SOAP is a lightweight protocol used to create web APIs, usually with Extensible Markup Language (XML). It supports a wide range of communication protocols across the internet, HTTP, Simple Mail Transfer Protocol (SMTP) and Transmission Control Protocol. The SOAP approach defines how a SOAP message is processed, the features and modules included, the communication protocols supported and the construction of SOAP messages. SOAP uses the XML Information Set as a message format and relies on application layer protocols, like HTTP, for message transmission and negotiation.
SOAP building blocks and message structure example
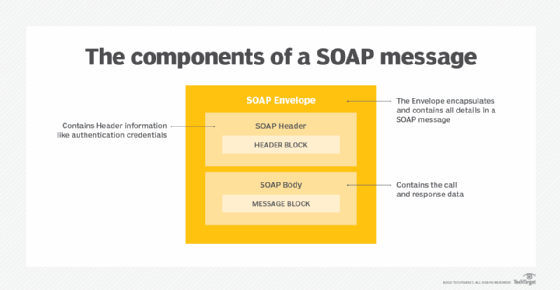
Simple Object Access Protocol, as a specification, defines SOAP messages that are sent to web services and client applications. SOAP messages are XML documents that are comprised of the following three basic building blocks:
- The SOAP Envelope encapsulates all the data in a message and identifies the XML document as a SOAP message.
- The Header element contains additional information about the SOAP message. This information could be authentication credentials, for example, which are used by the calling application.
- The Body element includes the details of the actual message that need to be sent from the web service to the calling application. This data includes call and response information.
The fault message is an optional fourth building block. If a SOAP fault is generated, it is returned as an HTTP 500 error. Fault messages contain a fault code, string, actor and detail.
How does SOAP work?
SOAP requests are easy to generate and process responses. First, a request for a service is generated by a client using an XML document. Next, a SOAP client sends the XML document to a SOAP server. When the server receives the SOAP message, it sends the message as a service invocation to the requested server-side application. A response containing the requested parameters, return values and data for the client is returned first to the SOAP request handler and then to the requesting client. Both SOAP requests and responses are transported using Hypertext Transfer Protocol Secure (HTTPS) or a similar protocol like HTTP.
SOAP advantages and disadvantages
SOAP is an integral part of the service-oriented architecture (SOA) and the web services specifications.
Advantages of SOAP include the following:
- Platform- and operating system-independent. SOAP can be carried over a variety of protocols, enabling communication between applications with different programming languages on both Windows and Linux.
- Works on the HTTP protocol. Even though SOAP works with many different protocols, HTTP is the default protocol used by web applications.
- Can be transmitted through different network and security devices. SOAP can be easily passed through firewalls, where other protocols might require a special accommodation.
Disadvantages, however, include the following:
- No provision for passing data by reference. This can cause synchronization issues if multiple copies of the same object are passed simultaneously.
- Speed. The data structure of SOAP is based on XML. XML is largely human-readable, which makes it fairly easy to understand a SOAP message. However, that also makes the messages relatively large compared to the Common Object Request Broker Architecture (CORBA) and its remote procedure call (RPC) protocol that will accommodate binary data. Because of this, CORBA and RPC are faster.
- Not as flexible as other methods. Although SOAP is flexible, newer methods, such as RESTful architecture, use XML, JavaScript Object Notation, YAML or any parser needed, which makes them more flexible than SOAP.
SOAP APIs
SOAP is a protocol that is almost always used in the context of a web services or SOA framework. As such, its API is typically hidden by the higher-level interface for SOA. SOA API middleware tools are available for nearly all modern programming languages, and Microsoft offers a variety of .NET SOAP and SOA tools.
SOAP vs. REST
SOAP is designed to break traditional monolithic applications down into a multicomponent, distributed form without losing security and control. In contrast, REpresentational State Transfer (REST) is a model of distributed computing interaction based on the HTTP protocol and the way that web servers support clients. REST over HTTP is almost always the basis for modern microservices development and communications. RESTful APIs use HTTP requests to GET, PUT, POST and DELETE data.
REST over HTTP is simple, flexible, lightweight and offers little beyond a way of exchanging information. SOAP can ride on HTTP as well, but it connects the elements of a complex set of distributed computing tools -- the web services and SOA framework -- as well as application components, and this forms a part of a total service-oriented framework.
Future of Simple Object Access Protocol
SOAP was the first widely used protocol for connecting web services in a service-oriented architecture. Today, modern development of distributed applications is largely based on RESTful principles. SOAP is almost always confined to legacy platforms. One area where SOAP is still in use is in applications that handle online transactions, as it's a style of API that is more rigid and protocol-driven.
Learn more about 10 API security guidelines, as well as how to choose between SOAP and REST here.







